Protecting your data. Securing your IP. Defending your Supply Chain
Last week, we participated at a seminar arranged by SOFF regarding exactly these topics. How to navigate data protection and cybersecurity requirements to be part of the US Government supply chain. We grasp every opportunity to participate in discussions and share our knowledge regarding how to ensure that we have a compliant defense supply chain.
It’s always a pleasure meeting fellow industry partners, like SAAB, BAE Systems, Nammo and Kitron and learning and discussing how they are manoeuvring in the cyber security landscape, protecting the data.
Criminal Prosecution
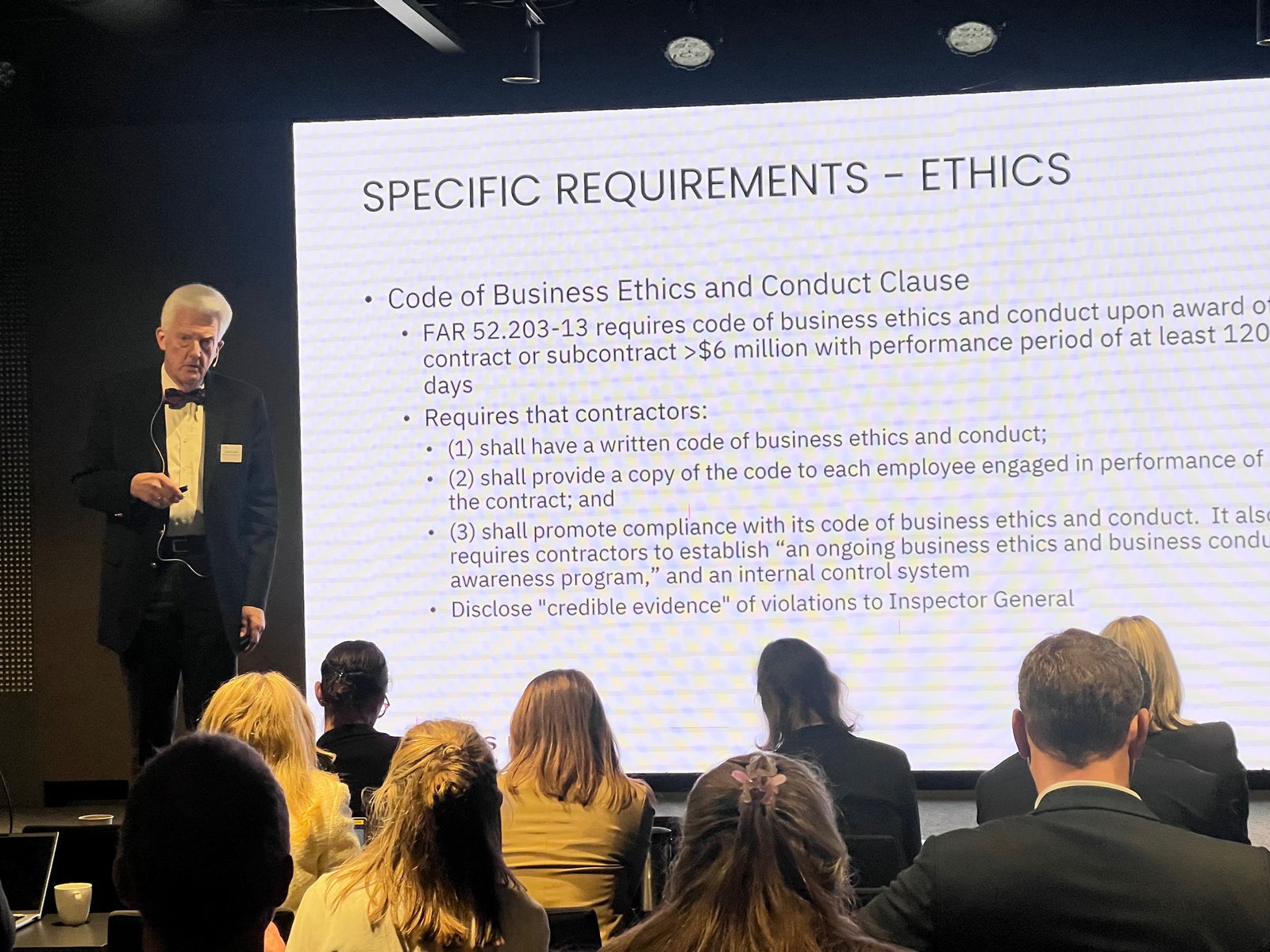
Protecting sensitive information and intellectual property (IP) within the defense supply chain is essential, as this sector faces unique challenges in data protection due to the highly classified nature of its operations. It is imperative to understand why and how we must safeguard IP, as well as how to secure a compliant supply chain, which is one of the key focus areas for Regulatory Technology (RegTech) companies, as CONFIDEE.
The risks and consequences for non-compliance are severe. Damaged reputation, breach of contract, cancellation of business, multimillion dollar fines which alone can destroy a company, government investigations, suspension from business, loss of business, criminal prosecution and personal risks, just mentioning some.
Then, how to avoid it?
It was said quite clearly during the SOFF event: Create the scenario that you do not want to happen. Test the system, use skilled people, understand the requirements, follow the export compliance regulations, train your personnel, involve the Board of Directors, as they are ultimately responsible, and repeat it all over again. Not to forget, involve partners that focus on, and actually know what compliance is, and how to address it. Ensure that they offer traceability, transparency and documentation of the process.
“The Kitchen Sink Approach”
Because, managing traceability and flowing down requirements in the supply chain is an ongoing challenge. It’s crucial to share necessary information, but sometimes, too much gets shared, leading to what is humorously called “The Kitchen Sink Approach.”
In simpler terms, this approach involves giving everyone in the supply chain loads of documents and requirements. Ironically, in trying to ensure compliance and securing your back, you might end up causing non-compliance. It highlights the need for a delicate balance in handling this process and a partner that knows what to flow down to whom.
The industry still has a job to do, educating the supply chain, taking responsibility and informing about what to flow down, why and to whom. Protecting the data.
Additional security practises
No cybersecurity seminar without discussions and presentations of CMMC (Cybersecurity Maturity Model Certification), the latest requirement being imposed by US DoD. CMMC is developed to enhance the cybersecurity practices of organizations in the defense industry. It expands and imposes further Controls beyond the current applicable standard NIST 800-171B to include additional security practices and maturity levels. Some seem to believe these requirements are new, the latest update is from 2019.
Defense regulations and being a compliant actor in the defense supply chain might sound complicated and challenging, it is. However, and, I will quote Kitron’s Hans Petter Thomassen describing Kitron’s journey to building data protection compliance: “How do you eat an elephant? One piece at the time”.
At CONFIDEE, compliance is our backbone. We are your Regulatory Technology Printed Circuit Partner, providing compliant printed circuits through our proprietary IT platform ID and our trusted suppliers. “For us, compliance is not a buzz word – it’s a way of managing our entire business”, and we grasp over it, piece by piece, like eating the elephant.